Firewall
The gateway has a firewall that provides four features:
Remote Management
Blocking Private IP address ranges
Blocking of virus DoS attacks
Blocking of peer-2-peer file sharing
Blocking of routers
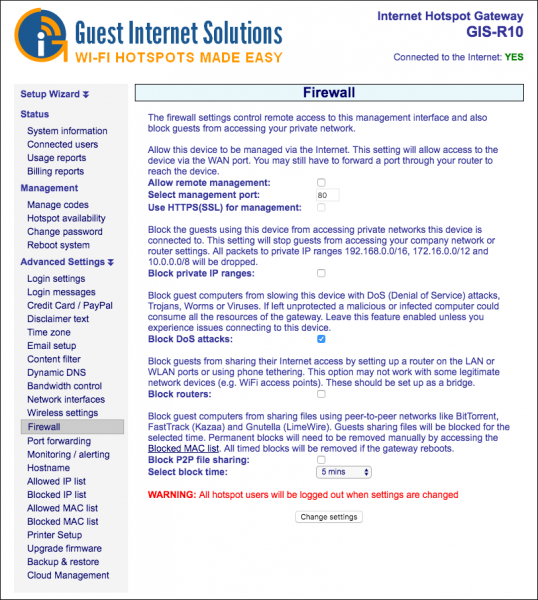
Remote Management
The Remote Management permits administrator login access via the Internet port to allow remote management of the gateway by opening the HTTP/HTTPS port.
By clicking the box to activate Internet port access the admin login is available on the Internet port by typing a fixed IP address into the browser.
The gateway can be administered from anywhere on the Internet providing that the business network has a fixed IP address and the business router has port forwarding.
Port forwarding is required from a device that owns the public facing IP address to a device that has a private (NAT) IP address.
If the GIS device gets a public IP then no port forwarding is required, if it gets an IP address in the range 192.168.X.X, 172.16.X.X, or 10.X.X.X then packets need to be forwarded for TCP port 80/HTTP (and 443 for HTTPS/SSL) on the public facing device to the GIS unit.
Blocking Private IP address ranges
Blocking Private IP address ranges prevents public Internet users accessing business computers in the network that the Internet (WAN) port is connected to.
This option is selected by default to ensure compliance with the recommendations of PCI DSS
Blocking of virus DoS attacks
Blocking of virus DoS attacks blocks any computer infected with a software virus or Trojan that is sending out a packet stream as part of a DoS (denial of service) attack.
If the computer is permitted to connect to the Internet then the service will become very slow for all users.
Therefore the default setting is to block infected computers.
Blocking of peer-2-peer file sharing
When"block P2P file sharing" is selected, it blocks any computer that has active torrent file sharing software.
By activating the P2P (peer to peer) blocking service the business can prevent any computer with P2P software from connecting to the Internet. A drop down menu permits the offending computer to be blocked for a period of time, or permanently.
We recommend that permanent blocking should be selected as a malicious user who is reconnected can use an encrypted service to share files, and encrypted communications cannot be detected.
Blocking of routers
Blocking of routers prevents the users from connecting a router and sharing their single use access code with multiple devices.
